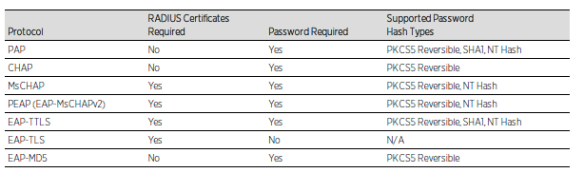
Using certificates is more secure than just using the username and password for authentication.

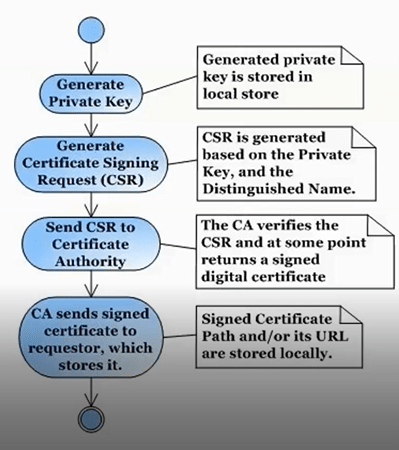
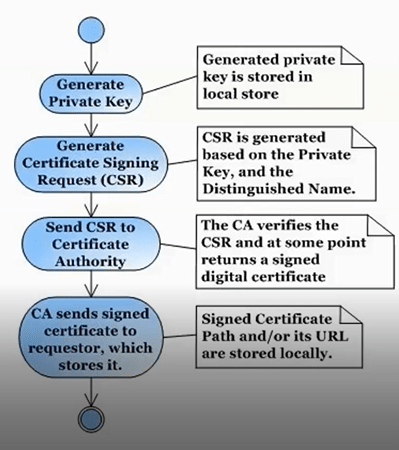
What is needed for Certificate:
Private key generated by CLI or Browser.
CSR generated by CLI or Browser.
CA will generate the certificate based on CSR through CLI or Browser.

Generate a Server Private Key
Use the following steps to generate an encrypted RSA private key.
1.Enter the following command to use OpenSSL to generate a password-encrypted PKCS #8 formatted server private key file. Use the key size and output file name you prefer. (If you are unsure of the key size, use 2048.)
openssl genrsa <key size> | openssl pkcs8 -topk8 -out <output file>
For example:
openssl genrsa 2048 | openssl pkcs8 -topk8 -out server.key
2.You will be prompted for an Encryption Password. Be sure to make a note of the password that you enter. If the password is lost, you will need to generate a new server private key and a new server certificate.


CN should use the FQDN of the ACE.
Create a Certificate Signing Request
Use the following steps to create a Certificate Signing Request (CSR).
1.Enter the following command to generate a CSR file. Use the output file name you used in step 1 above as the input file, and specify the output file name you prefer:
openssl req -new -key <input file> -out <output file>
For example:
openssl req -new -key server.key -out server.csr
2.You will be prompted for information that will appear in the certificate. When you are prompted for a Common Name, specify the fully qualified host name of the NAC appliance. For example:
Common Name (eg, YOUR name) []:nac1.mycompany.com
If you are creating a client and/or server certificate CSR request for use with PEAP or EAP-TLS, you may need to add an extension to the command used to generate the CSR file. Server and client certificates require an extension in order to operate as intended. Verify with your certificate vendor whether they require that the extensions are part of the CSR or are included in the certificate when the request is made. The following are command examples of the CSR request that include each of the extension options available.
•If the CSR is for the NAC appliance, the command must include:
openssl req -new -reqexts server_auth -key <input file> -out <output file>
•If the CSR is for a client, the command must include:
openssl req -new -reqexts client_auth -key <input file> -out <output file>
•If the CSR is for both the NAC appliance and client, the command must include:
openssl req -new -reqexts server_and_client_auth -key <input file> -out <output file>

Verify CSR by openSSL:
openssl req -text -noout -verify -in <csrfile.csr>
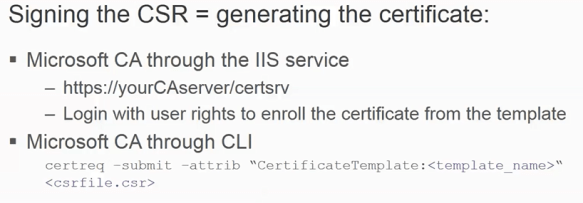
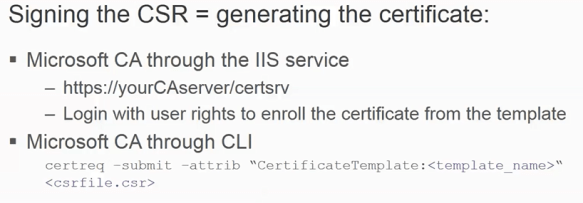
Submit the Request to a Certificate Authority
The procedure for submitting a CSR to a Certificate Authority (CA) varies with the service used. Usually, it is done through a website using a commercial service such as VeriSign. You can also use an in-house CA, which generates certificates used internally by your enterprise. You will provide information including the contents of the CSR, and receive back one or more files containing the server certificate and possibly other certificates to be used in a chain.









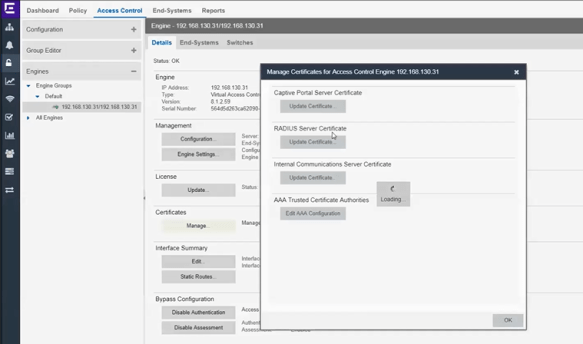
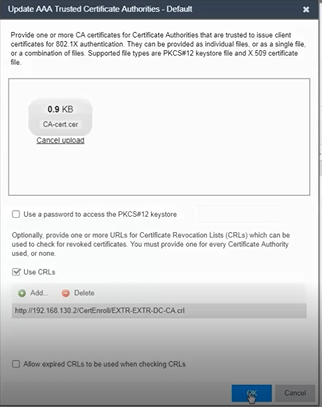
Install certificate to client computer by GPO which is transparent for users. There should be a user certificate (in Certificates – Current User : Personal>Certificates) and a CA certificate installed (in Trusted Root Certificate Authorities) on the client.
Note: Some browsers may prevent you from seeing and choosing different settings such as key length when asking for the User certificate. Verify the certificate is installed using run mmc and add certificates snap-in. Also open the installed certificate and look at the details to gather more detail.
 Note: This was helpful for the XP test machine I was using.
Note: This was helpful for the XP test machine I was using.